
Generated AI image by Microsoft Bing Image Creator
If you’re like me, and you’ve built several Github repositories over time as part of developer learning fun projects, there’s probably a good chance these same repositories will not get maintained on some form of regular basis.
The reasons for this to happen can be wide-ranging - everything from being too busy at work, changing interests for different software frameworks, lifestyle priorities changes, changing career responsibilities etc, etc - there’s too many to list here.
They took the best of our coding life as months or years go by.
As a consequence, your Github repositories do become quickly stale over time.
This ‘staleness’ - come with old dependencies that do not get updated, which at worse, could be leaking software security issues over time.
I have over 50 repositories in my Github profile and there’s no way that I could keep track of knowing which repos have more security holes to address after another, let alone have to fix up security vulnerabilities dependencies one PR at a time on my own… 😨
Thus I need to find a way to auto-manage all these repositories without lifting a finger (much)
Without further ado, I found this useful toolchain from Github marketplace - Snyk.

Synk is an open-source tool that helps developers track, find and fix security vulnerabilities across all of your Github projects.
According to this page, as it describes as -
- Finds vulnerabilities by scanning your repos using its transitive database to match their vulnerabilities behind them
- Fix their vulnerabilities by auto-generating a new PR that will be recommended the patches around those vulnerabilities hole.
- Prevents vulnerabilities by running their suite of tests on those same PRs and prevent the vulnerabilities from merging to your PR
- It offers continuous monitoring on Github repos so you can respond quickly as you need on a daily basis.
This all sounds pretty awesome!
This is the type of thing I will like to include as my software toolchain to know where my repos are going wrong or not. So I don’t have to manually install things myself.
What a great boon to keep my repos and clean and fresh!
Best of all - it is absolutely free! You can do this on unlimited Github repos you have in your portfolio. It comes with its own special CI/CD pipeline as well.
To start with,
- You open up the enable tool-chain from Marketplace.
- Snyk scanner pipeline is monitoring all of your Github repos.
- Then you will get the Snyk emails to do look at them.
Once you have all that setup, you will eventually arrive at this dashboard screen.
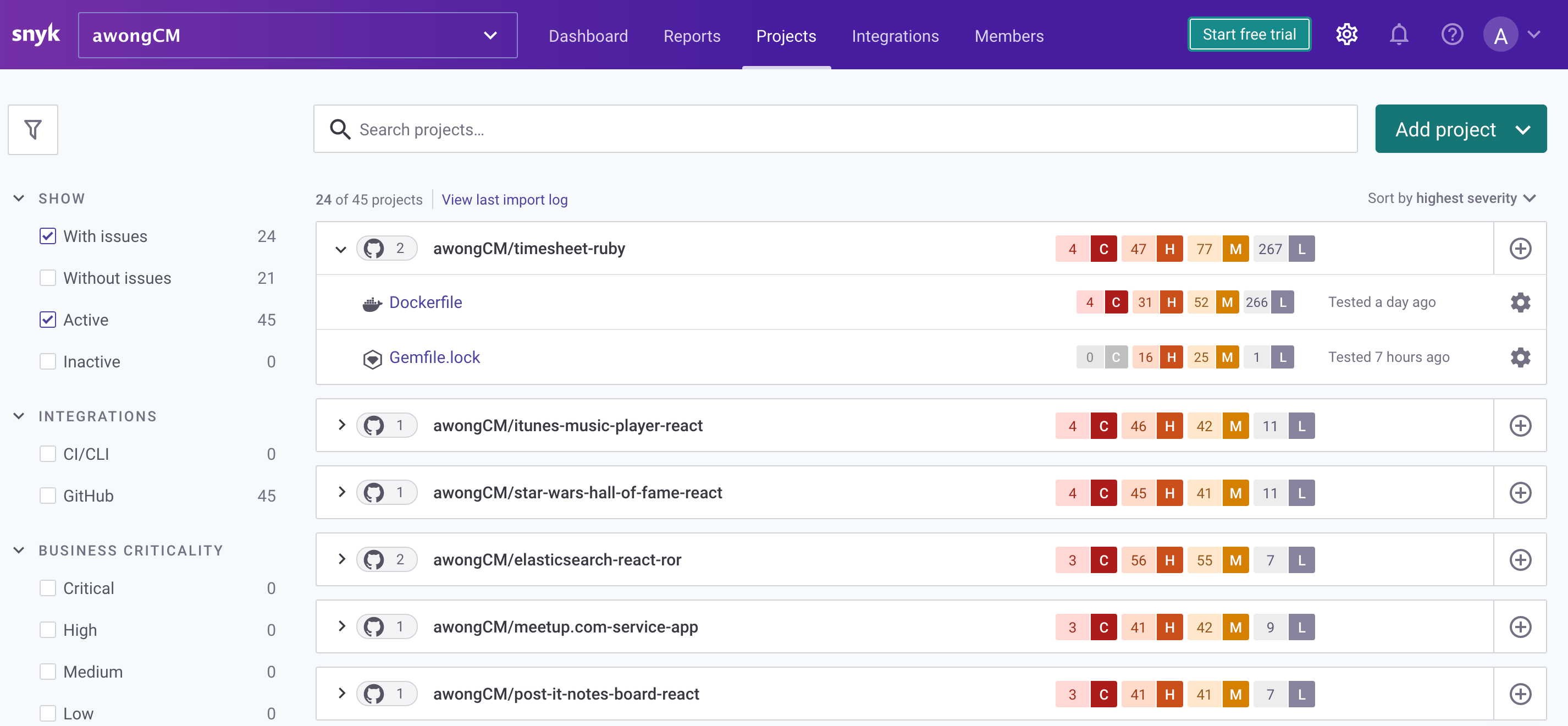
There it is - my one-stop landing page to monitor and assess the state of my Github repos’ dependencies health check on security vulnerabilities.
Like all things of security audit and vulnerability checks as you would do with anti-virus and anti-Malwarebytes check, we have to make our own informed choices whether we should triage and resolve these vulnerabilities urgently or not, depending on their level of severity as well the broadness of their impacts to their entire health state of the app’s core functionality.
Once you decide when you want to resolve these vulnerabilities with ease, Snyk’s give you this option to create open PR to one of your nominated repos, and it will self-generate the best security patch algorithm for you and will apply these patches should you decide to accept their security recommendation by merging.
For eg, I recently did one of the security patches not long ago on one of my old Node repos, which I haven’t touched for some considerable time.
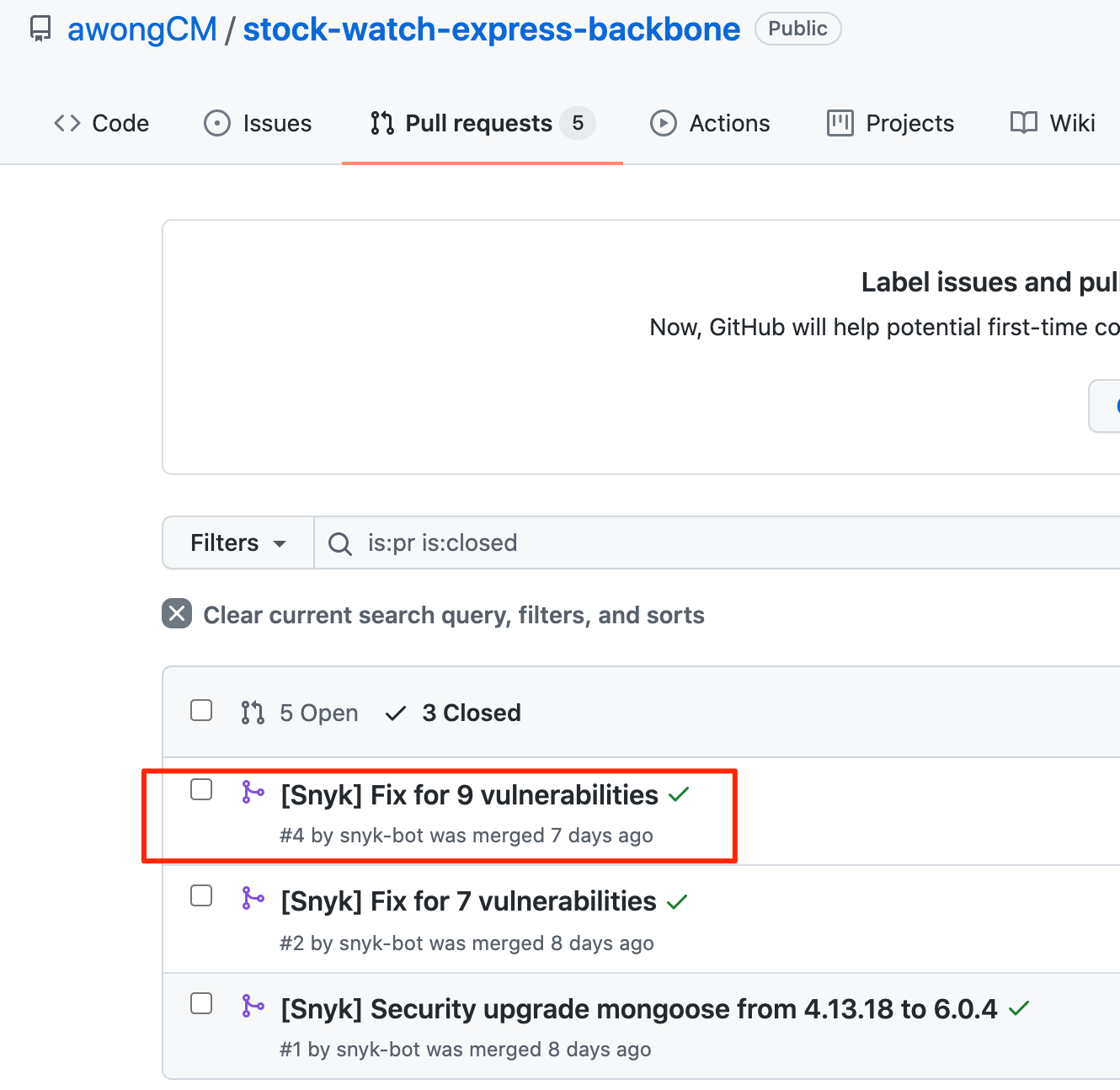
If I open up the merged PR.
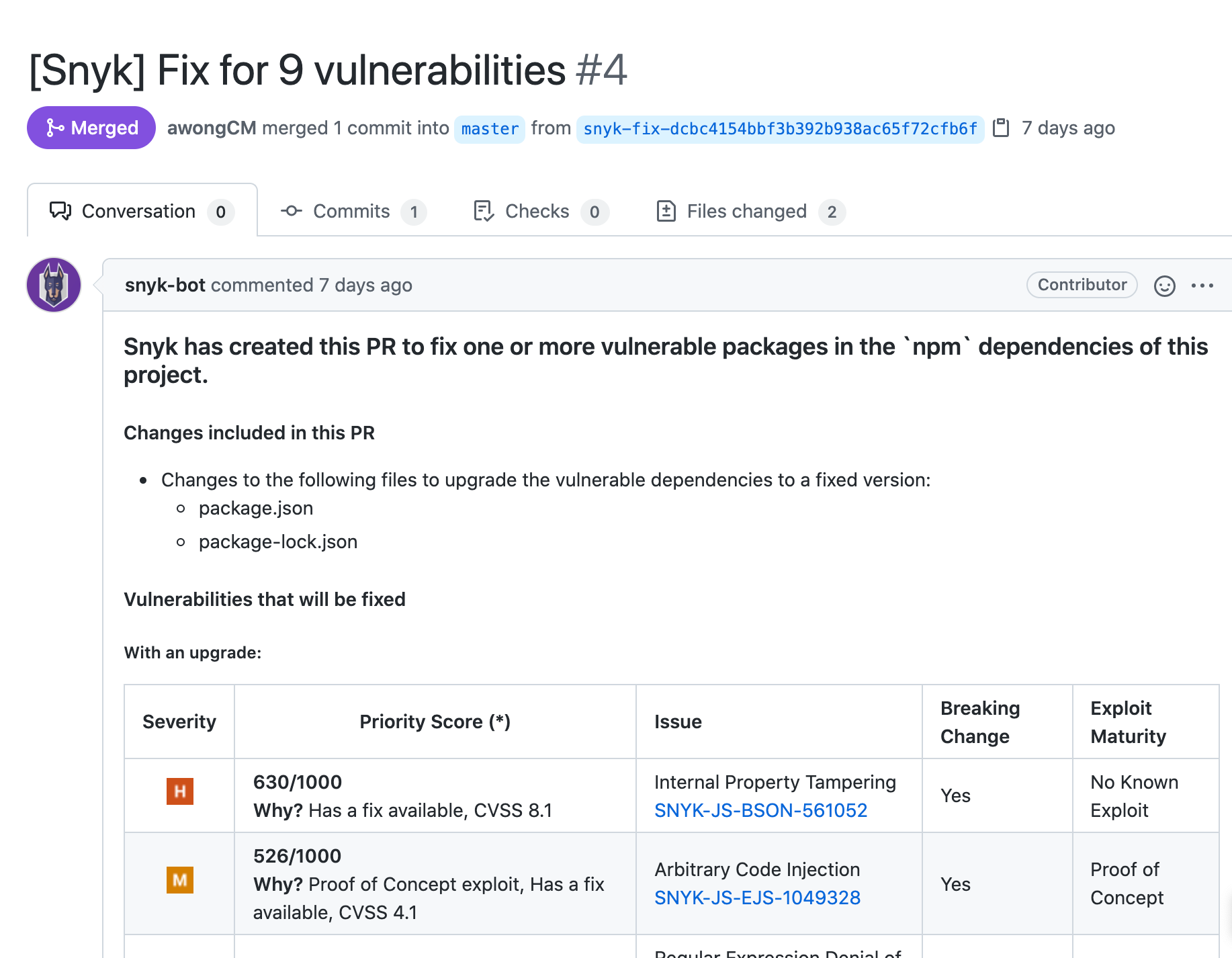
Here you can see a table generated by Snyk outlining explanations of which files suffered security vulnerabilities and came up with recommended fixes for these.
If you click on the ‘’Files Change’ tab, you notice the following:
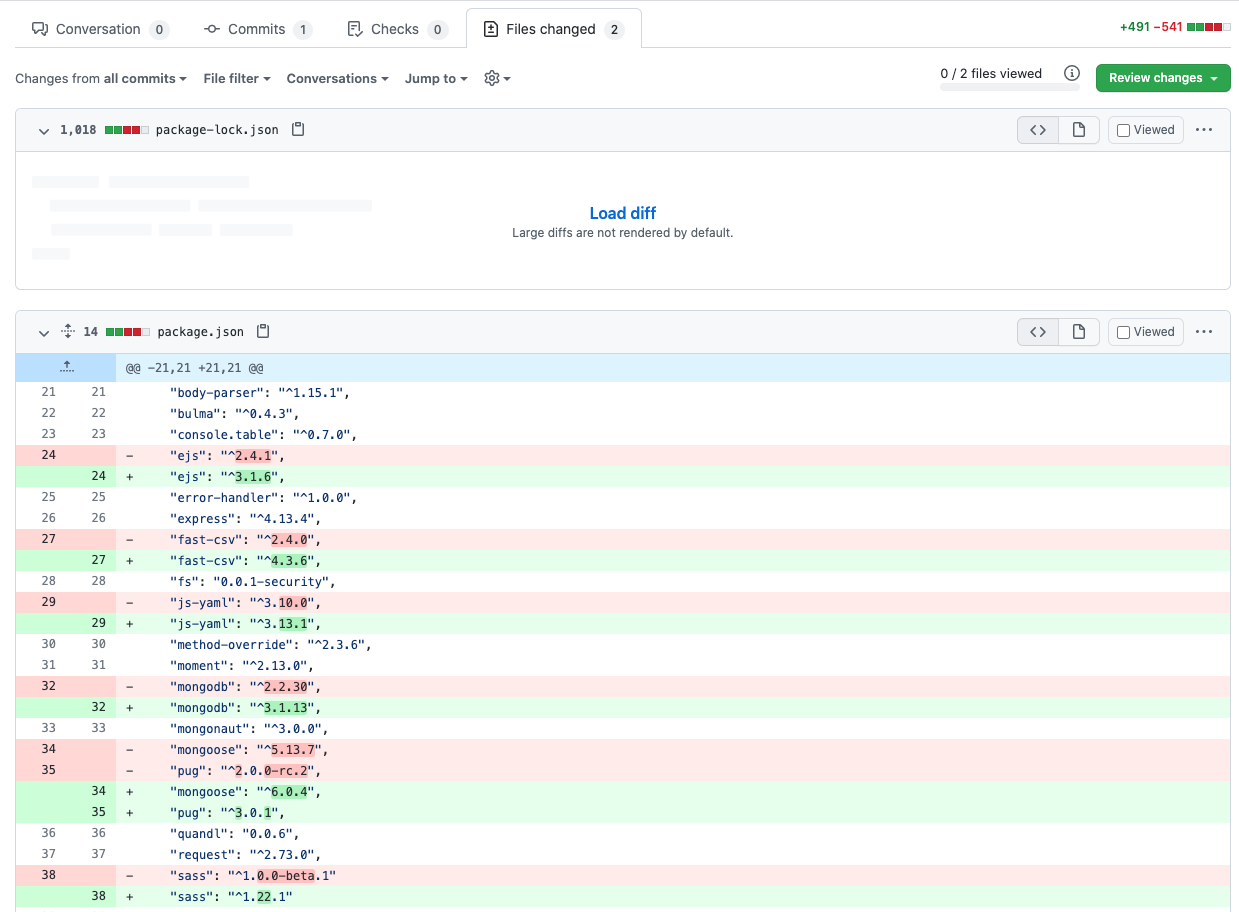
It forewarns that these are affected npm libaries that need to be upgraded at their latest working version whose security patches will be applied.
That’s it!
All of the thought of manually checking and verifying package libraries’ vulnerabilities by myself not became a major headache to deal with.
I have the available tools that help to automate that workflow process for me - without doing any heavy finger lifting!
This is precisely what I love about it. 😎
Go ahead, reap and sow the power of free open source software that’s built by the community that rests on the shoulder of giants!🤞🤞👨💻👩💻
Till next time, Happy Coding!